Documentation Index
Fetch the complete documentation index at: https://docs.hel.io/llms.txt
Use this file to discover all available pages before exploring further.
To get started with Webhooks, check out our API Reference for full details.
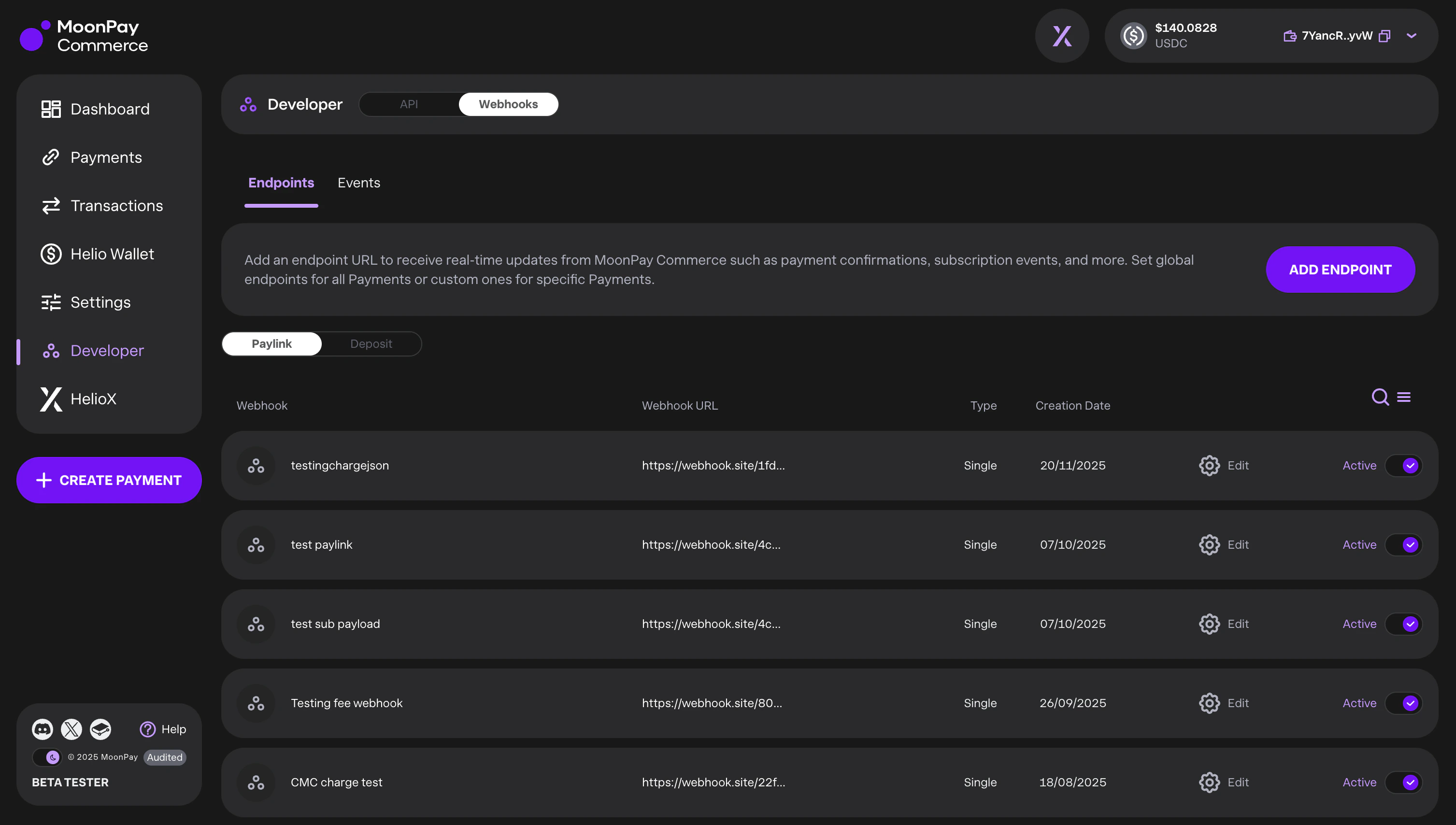
Configuration
You can create and manage webhooks via the API or the Dashboard (Developers → Webhooks). We support two event types:depositId: Events related to customer deposits.paylinkId: Events related to specific checkout links.
Webhook Scope
For both event types, you can configure the scope of the notifications:- Global: Receive events for all IDs associated with your company account.
- Resource-Specific: Receive events only for a specifically defined
depositIdorpaylinkId.
Monitoring & Retries
The Dashboard provides full visibility into your webhook health:- Event Logs: View triggered events, delivery statuses, and timestamps.
- Retry Logic: We automatically attempt redelivery up to 12 times.
- Manual Replay: If the automatic retry limit is reached, you can manually trigger a replay from the event log.
Webhook Security
Every webhook request sent by MoonPay Commerce includes two layers of authentication:- Bearer Token — An
Authorization: Bearer <sharedToken>header that confirms the request originates from MoonPay Commerce. - HMAC Signature — An
X-Signatureheader containing an HMAC-SHA256 hex digest of the request body, keyed with the samesharedToken. This guarantees the payload has not been tampered with in transit.
The
sharedToken is generated when you create a webhook and is returned only once. Store it securely — you will need it to verify incoming webhook signatures. For the full list of headers included with each webhook delivery, see the Webhook Request Headers in the API Reference.Verifying Webhook Signatures
When your server receives a webhook, you should verify theX-Signature header to confirm payload integrity. Here is how:
- Extract the
X-Signatureheader from the incoming HTTP request. - Read the raw request body as a string (before any JSON parsing that might reorder keys).
- Compute the HMAC-SHA256 digest of the raw body using your
sharedTokenas the key. - Compare your computed signature with the
X-Signaturevalue using a timing-safe comparison.